Popping shell in a hospital
…ok, it’s almost popping shell.
A few months ago, a family member was in the hospital for surgery. The hospital, New York Presbyterian, had courteously set up a computer for family members to use. However, it was running Windows XP, which is a no-longer-supported security nightmare.
Curious, I decided to investigate.
They’d disabled nearly everything. No “run” box, no explorer, nothing except an outdated copy of IE, and Office 2003. In the “Open” dialog, nearly every folder was empty. All modifications are dumped at logoff.
So, all the easiest ways to pop shell on this security nightmare are blocked off. They at least made some effort to secure things. It’s time to look into the wonderful rabbit hole that is Excel.
The wonderful thing about Excel is that it’s extremely flexible: Even an ancient version of Office (2003, which is what they had) can embed ActiveX controls, it can run Visual Basic, it can attach any of the Windows common controls as inputs to individual cells, and many other things.
The dangerous thing about Excel is (also) that it’s extremely flexible: Every single feature increases the attack surface, and exponentially complicates security.
In this case, the ability to embed a hyperlink is the most useful feature for me. Because of the way Windows Explorer/Windows Shell works, we can point a hyperlink at a local file, and the shell will execute the action associated with that file. If the file is an html file, Windows will open it in IE; if it’s a txt file, Windows will open it in Notepad; if it’s an exe file, Windows will execute it. I think you can see where I’m going with this.
When I attempted to “customize” the link, excel popped a version of the Common File Dialog… but all accessible folders were empty!
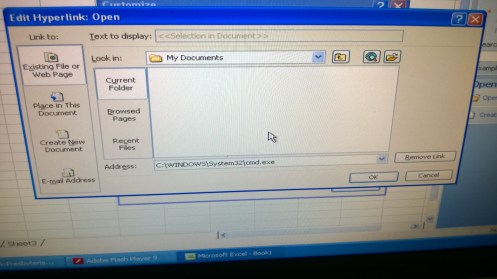
The “My Documents” folder, like every other browsable location, is devoid of clickable items.
So they’ve clearly tried to shrink the attack surface by hiding every clickable file, which has some value.
But again, Windows Shell link/path handling features are here to help me sneak past their security.
If you type the full path to a file in the “Address” field (or, more generally, the “Name” field), and then click OK (or, “Open”/”Save”), Windows accepts the (valid) path, and closes the dialog.
Opening the link then executes cmd.exe:
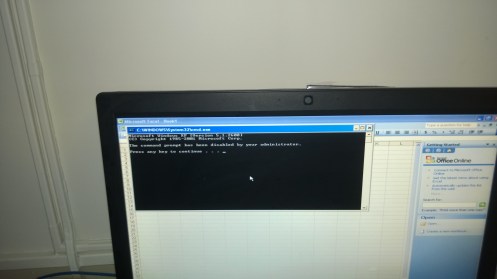
Tada! Command prompt opened… kinda
They (thankfully) have “disabled” the command prompt, which means I can’t easily use it to do any harm. There’s probably a way around it, but I was satisfied with getting CMD.exe to execute at all, and so I went on my way.

